“Actors are leveraging multiple open source tools that alter the signature date of kernel-mode drivers to upload malicious and unverified drivers signed with expired certificates,” Cisco Talos said in a full two-part report shared with The Hacker News . “This is a huge threat, as kernel access provides full access to a system, and therefore full compromise.”
Following the responsible disclosure, Microsoft said it took steps to block all certificates to mitigate the threat. It further stated that its investigation found that “activity was limited to abuse of multiple developer program accounts and that no Microsoft account compromise was identified.”
The tech giant, in addition to suspending the program accounts of the developers involved in the incident, emphasized that the threat actors had already obtained administrative privileges on the compromised systems prior to the use of the drivers.
It’s worth noting that the maker of Windows implemented similar lockdown protections in December 2022 to prevent ransomware attackers from using Microsoft-signed drivers for post-exploit activity.
Driver signature enforcement, which requires kernel-mode drivers to be digitally signed with a certificate from the Microsoft Developer Portal, is a crucial line of defense against malicious drivers, which could be weaponized to evade patch fixes security, alter system processes, and maintain persistence. The policy change was introduced with the debut of Windows Vista.
The new vulnerability discovered by Cisco Talos makes it possible to forge signatures on kernel-mode drivers, allowing them to bypass Windows certificate policies.
This is possible thanks to an exception created by Microsoft for compatibility, which allows cross-signed drivers if the computer was upgraded from a previous version of Windows to Windows 10, version 1607; Secure Boot is disabled in the BIOS; and the controllers were “signed with an end-entity certificate issued before July 29, 2015 that links to a cross-signed [certification authority].”
“The third exception creates a loophole that allows a newly compiled driver to be signed with non-revoked certificates that were issued or expired before July 29, 2015, provided that the certificate is from a supported cross-signed certificate authority,” the cyber security company said.
As a result, drivers signed in this manner will not be prevented from loading on Windows devices, enabling threat actors to take advantage of escape clauses to deploy thousands of malicious, unsigned drivers without submitting them to Microsoft for verification.
These rogue drivers have been deployed using signature timestamp forging software such as HookSignTool and FakeCertifyTimeValidity, which have been publicly available since 2019 and 2018, respectively.
HookSignTool has been accessible via GitHub since January 7, 2020, while FuckCertVerifyTimeValidity was first committed to the code hosting service on December 14, 2018.
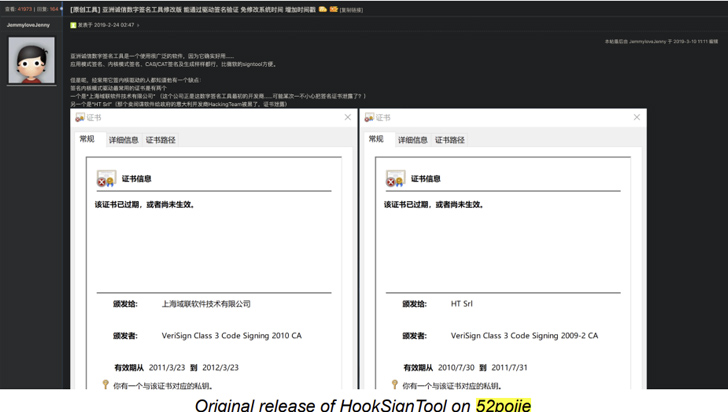
Cisco Talos explained, “HookSignTool is a driver signature forging tool that, through a combination of hooking into the Windows API and manually altering the import table of a valid code signing tool, changes the signature date of a driver during the signing process.”
Specifically, this includes hooking up the CertVerifyTimeValidity function, which verifies the time validity of a certificate, to replace the signature timestamp during execution.
The GitHub page for Nonsense Certificate Verification Time Validity reads “This small project prevents SignTools from verifying the validity of certificate times and lets you sign your bin with an old certificate without manually changing the system time.”
“This installs the hook to crypt32!CertVerifyTimeValidity and makes it always return 0 and kernel32!GetLocalTime returns what you want because you are in the command line of signtools for signing certificates from year 2011” -fuckyear 2011 Can add “put”.
As noted, a successful forgery requires a non-revoked code signing certificate that was issued before July 29, 2015, along with the certificate’s private key and passphrase.
Cisco Talos said it discovered more than a dozen code signing certificates, including keys and passwords, in a PFX file hosted on the FuckCertVerifyTimeValidity forked repository on GitHub. It was not immediately clear how these certificates were obtained.
In addition, it has been observed that HookSignTools has been used to re-sign cracked drivers to bypass Digital Rights Management (DRM) integrity checks, an actor named “Juno_Junior” accessed the primo cache. Has released a cracked version, which is a legitimate software caching solution, on 9 November 2022 in a Chinese software cracking forum.
Talos researchers said, “In the cracked version […], the patched driver was re-signed with a certificate originally issued to ‘Shenzhen Luyoudashi Technology Co. Ltd.'”. “This ability to resign a broken driver removes a significant barrier when attempting to bypass a DRM check in an unsigned driver.”

He is not everything. HookSignTool is also being used by a previously unknown driver identified as RedDriver to generate its signing timestamp. Active since at least 2021, it operates as a driver-based browser hijacker that takes advantage of the Windows Filtering Platform (WFP) to intercept browser traffic and reroute it to localhost (127.0.0.1).
The target browser is randomly selected from a hard-coded list that includes the process names of several popular Chinese language browsers such as Libao, QQ Browser, Sogou and UC Browser as well as Google Chrome, Microsoft Edge and Mozilla Firefox.
“I initially found RedDriver while researching certificate timestamp forging on Windows drivers,” Chris Neal, Outreach Researcher at Cisco Talos, told The Hacker News. “This was one of the first samples I immediately suspected. What caught my attention was the list of web browsers stored inside the reddriver file.”
The ultimate purpose of this browser traffic redirection is unclear, although it goes without saying that such capability can be abused to tamper with browser traffic at the packet level.
The RedDriver infection chain begins with the execution of a binary named “DnfClientShell32.exe”, which, in turn, initiates encrypted communication with a command-and-control (C2) server to download the malicious driver.
Neil said, “We did not observe the delivery of the initial file, but it is quite possible that the file was packaged to disguise itself as a game file, and hosted on a malicious download link.” “The victim probably thought they were downloading a file from a legitimate source and ran the executable. ‘DNFClient’ is the name of a file belonging to ‘Dungeon Fighter Online’ which is a hugely popular game in China and is commonly known as It’s called ‘DNF’.
“The RedDriver was likely developed by highly skilled threat actors because the learning curve for developing malicious drivers is steep,” Cisco Talos said. “While the threat appears to target native Chinese speakers, the authors are likely Chinese speakers as well.”
“The authors also demonstrated familiarity or experience with the software development lifecycle, another skill set that requires previous development experience.”
The development comes as Sophos said it found more than 100 malicious kernel drivers that were signed by Microsoft and other companies, some dating back to April, and either prevent security software from running as designed Were or capable of acting as a stealth rootkit. Monitoring network traffic using WFP.
“It appears that the creator of the malicious driver created a ‘parent’ version of the driver, then ran the parent version through one or more packer utilities one or more times, in some cases creating dozens of ‘child’ variants, of which All “manufacturers can submit to Microsoft for signature,” said Andrew Brandt, researcher at Sophos.
“There are a lot of advantages for threat actors to deploy drivers in their infection chain, although they are much more difficult to develop than user-mode malware,” Neil said. “The drivers for EDR are hard to detect and difficult to analyze, especially if any obfuscation is employed.”
