The US Cyber Security and Infrastructure Security Agency (CISA) and “The threat landscape in 5G is dynamic; because of this, network slicing over time will require advanced monitoring, auditing, and other analytical capabilities to meet certain levels of service level requirements.” National Security Agency (NSA) said.
5G is the fifth-generation technology standard for broadband cellular networks, providing increased data speeds and lower latency. Network slicing is an architectural model that allows mobile service providers to partition their networks into multiple independent “slices” to create virtual networks that cater to different customers and use cases.
The latest advice builds on guidance previously issued by the agencies in December 2022, which warned that network slicing could expose users to a variety of threat vectors – denial of service, jamming, identity theft, and So many. -Opponent attacks in between. Effectively hindering the confidentiality, integrity and availability of network services.
A report published by Enea AdaptiveMobile Security in March 2021 detailed concerns about 5G network slicing, describing it as a way to gain malicious access to slices and orchestrate denial-of-service attacks against other network functions. The method has been described. -The ability of force attacks has been highlighted.
Then in May 2021, the US government warned that inadequate implementation of telecommunications standards, supply chain threats and vulnerabilities in system architecture could pose major cyber security risks to 5G networks, allowing threat actors to extract valuable intelligence from victims. Will be allowed to take advantage of loopholes.
In the latest guidance, officials cited denial-of-service attacks, misconfiguration attacks and man-in-the-middle attacks on signaling aircraft as three key 5G threat vectors, noting that a zero trust Secure Network Deployment Architecture (ZTA) can help.
“A large portion of ZTA can be accomplished by employing Authentication, Authorization, and Audit (AAA) techniques,” CISA and the NSA said.
Authentication and authorization can also reduce threat vectors resulting from misconfiguration attacks.”
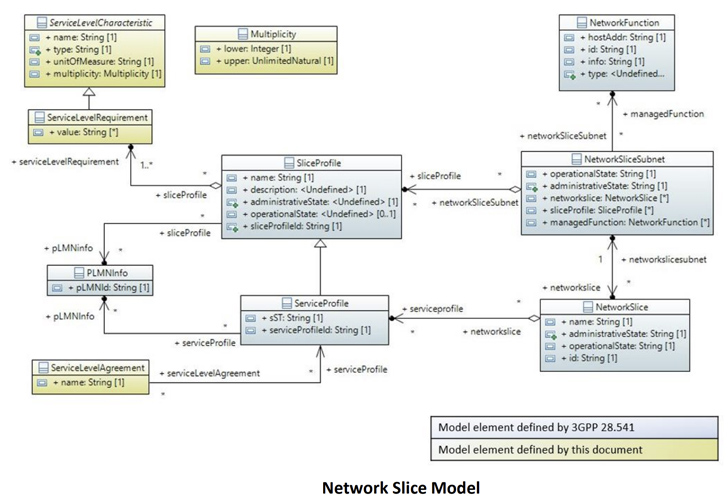
The agencies also called for industry-recognized best practices for how 5G network slicing can be implemented, designed, deployed, operated, and maintained. These are important to identify, as they can affect quality of service (QoS) and service level agreements (SLAs).
