Threat actors are taking advantage of a technique called versioning to avoid the Google Play Store’s malware detection and target Android users.
“Campaigns using versioning typically target users’ credentials, data, and finances,” the Google Cyber Security Action Team (GCAT) said in an August 2023 Threat Horizons report shared.
Although versioning is not a new phenomenon, it is covert and difficult to detect. In this method, a developer releases an initial version of an app on the Play Store that passes Google’s pre-publication checks, but is later updated with a malware component.
This is achieved by pushing an update from an attacker-controlled server to serve malicious code to the end user device using a method called dynamic code loading (DCL), effectively turning the app into a backdoor.
Earlier this May, ESET discovered a screen recording app called “iRecorder – Screen Recorder” that was first uploaded to the Play Store before malicious changes were introduced to secretly spy on its users. The latter remained harmless for about a year.
Another example of malware that uses the DCL method is Sharkbot, which repeatedly appears on the Play Store as a security and utility app.
SharkBot is a financial Trojan that initiates unauthorized money transfers from compromised devices using the Automated Transfer Service (ATS) protocol.
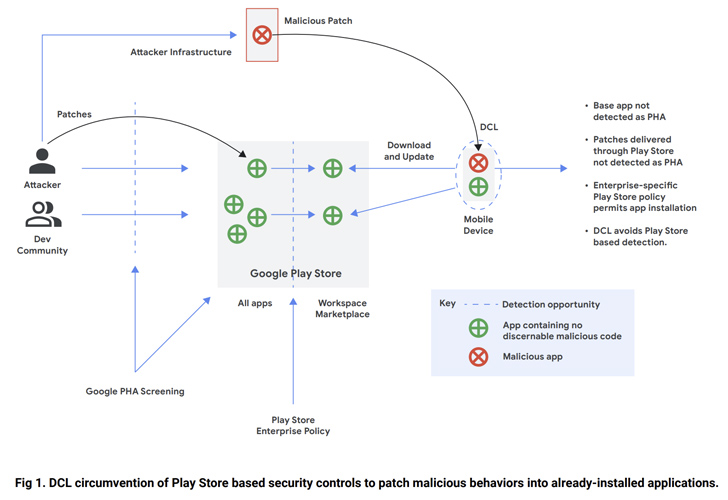
Dropper applications that appear on storefronts come with reduced functionality that, once installed by victims, download the full version of the malware to attract less attention.
“In enterprise environments, versioning demonstrates the need for defense-in-depth principles, including limiting application installation sources to trusted sources such as Google Play or managing corporate devices through a mobile device management (MDM) platform, but It is not limited to these only,” the company said.
The findings come after ThreatFabric revealed that according to KrebsOnSecurity, malware spreaders are exploiting a bug in Android to disguise malicious apps as benign by “corrupting the app’s components”, so that the entire app remains valid.
The Dutch cyber security company noted in June, “Actors may have multiple apps published in the store at the same time under different developer accounts, however, only one is acting as malicious, while the other is a backup,” is to be used after takedown.”
“Such a strategy helps actors maintain very long campaigns, reducing the time needed to publish another dropper and continue the distribution campaign.”
To mitigate any potential risks, it is recommended that Android users stick to trusted sources for downloading apps and enable Google Play Protect to receive notifications when potentially harmful apps (PHAs) are found on the device.
