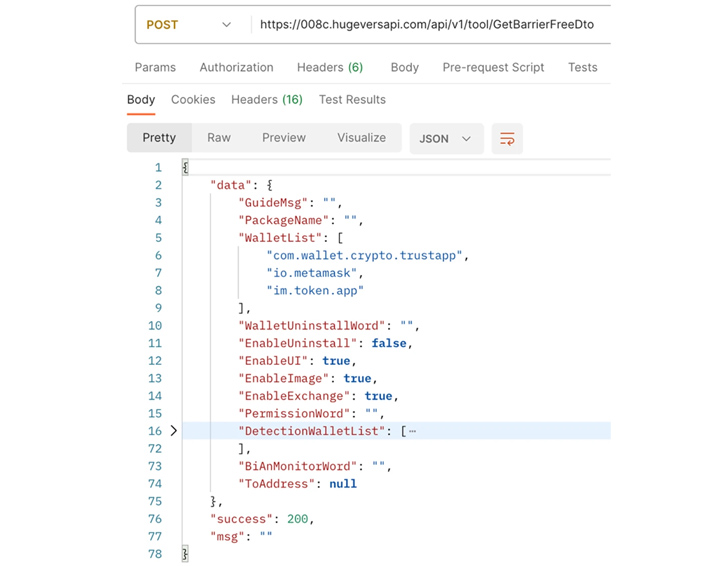
According to Trend Micro, CherryBlos is distributed through fake posts on social media platforms and comes with the capabilities to steal credentials related to cryptocurrency wallets and when a victim copies a string matching a predefined format to the clipboard. If so, the wallet acts as a clipper to replace the address.
Once installed, apps ask for users’ permission to grant it accessibility permissions, which allows it to automatically grant additional permissions as needed. As a defense evasion measure, users who attempt to force close or uninstall the app by entering the Settings app are sent back to the home screen.
In addition to displaying fake overlays on top of legitimate crypto wallet apps to steal credentials and transfer fraudulent funds to attacker-controlled addresses, CherryBlos uses OCR to recognize potentially memorable phrases from images and photos stored on the device, The results of which are uploaded from time to time.
The success of the campaign is based on the possibility that users take screenshots of wallet recovery phrases on their devices.
Trend Micro said it also found an app developed by CherryBlos threat actors on the Google Play Store, but it did not contain any malware. An app called SynthNet has been removed by Google.
It appears that the threat actors share overlap with another activity set, which includes 31 fraudulent money-making apps, called FakeTrade, based on the use of shared network infrastructure and app certificates, which are official websites. Apps are hosted on the Marketplace.
Most of the apps were uploaded to the Play Store in 2021 and have been found targeting Android users in Malaysia, Vietnam, Indonesia, Philippines, Uganda and Mexico.
“These apps claim to be e-commerce platforms that promise enhanced income for users through referrals and top-ups,” Trend Micro said. “However, users will be unable to withdraw their funds when they attempt to do so.”
The disclosure comes as McAfee details an SMS phishing campaign against Japanese Android users posing as an electricity and water infrastructure company to infect devices with malware called Spynote. The campaign takes place in early June 2023.
“After launching the malware, the app opens a fake settings screen and prompts the user to enable accessibility features,” McAfee researcher Yukihiro Okutomi said last week.
“By allowing the Accessibility Service, the malware disables battery optimization so that it can run in the background and automatically allows unknown source installations to install other malware without the user’s knowledge.”
It’s no wonder that malware writers are constantly looking for new ways to lure victims and steal sensitive data in the ever-evolving cyber threat landscape.
Google, last year, began taking steps to prevent abuse of the Accessibility API by rogue Android apps to covertly collect information from compromised devices by preventing sideloaded apps from using accessibility features Could.
But stealers and shredders represent just one of many types of malware – such as spyware and stalkerware – that are used to track targets and gather information of interest, which infringes on personal privacy and security.
New research published this week found that a surveillance app called SpyHide has been secretly collecting private phone data from around 60,000 Android devices around the world since at least 2016.
A security researcher who says, “Some users (operators) have multiple devices linked to their account, some have more than 30 devices that they have been monitoring for years and spying on everyone in their lives.” Maia said in the name of arson crimew.
It is therefore important for users to be cautious when downloading apps from unverified sources, verify developer information, and check app reviews to mitigate potential risks.
The fact that no one can stop threat actors from creating fake developer accounts on the Play Store to distribute malware has not gone unnoticed by Google.
Earlier this month, the search giant announced that it would require all new developer accounts that register as an organization to have valid D-U-N-S specified by Dun & Bradstreet before submitting apps in an effort to build user trust. Number will need to be provided. This change will be effective on August 31, 2023.
