Malicious ads served inside Microsoft Bing’s artificial intelligence (AI) chatbot are being used to deliver malware while searching for the popular tool.
The findings come from Malwarebytes, which revealed that unsuspecting users can be duped into visiting silly sites and installing malware directly from Bing Chat conversations.
Introduced by Microsoft in February 2023, Bing Chat is an interactive search experience powered by OpenAI’s large language model GPT-4. A month later, the tech giant began exploring advertising in conversations.
But the move has also opened the door to threat actors who resort to malicious tactics and propagate malware.
“Ads can be inserted into Bing Chat conversations in a variety of ways,” said Jerome Segura, director of threat intelligence at Malwarebytes. “One of them is when a user hovers over a link and an ad is displayed before the organic result.”
In an example highlighted by the cybersecurity vendor, a Bing Chat query to download a legitimate software called Advanced IP Scanner returned a link that, when hovered, displayed a malicious ad pointing to a fraudulent link before the official site hosting the tool.
Clicking the link takes the user to a traffic direction system (TDS) that fingerprints and determines if the request is actually originating from a real human (as opposed to a bot, crawler, or sandbox), before taking them to a decoy page containing the rogue installer.
The installer is configured to run a Visual Basic script that beacons to an external server with the potential goal of receiving the payload of the next stage. The exact nature of the malware distributed is currently unknown.
A notable aspect of the campaign is that the threat actor managed to infiltrate the advertising account of a legitimate Australian business and create advertisements.
“Threat actors continue to leverage search ads to redirect users to malicious sites hosting malware,” Segura said. “With credible landing pages, victims can be easily tricked into downloading malware and be no one the wiser.”
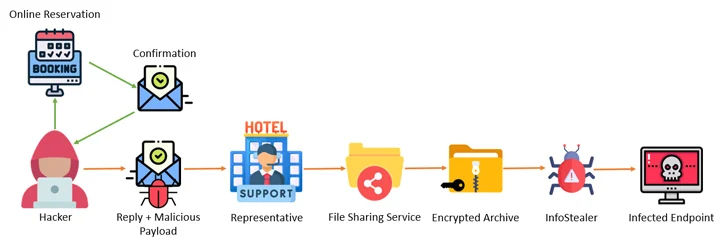
The revelation comes as Akamai and Perception Point uncovered a multi-step campaign that entails attacking the systems of hotels, booking sites, and travel agencies with information stealer malware and then leveraging the access to the accounts to go after financial data belonging to customers using fake reservation pages.
“The attacker, masquerading as the hotel, reaches out to the customer through the booking site, urging the customer to ‘re-confirm their credit card,’ then steals the customer’s information,” Akamai researcher Shiran Guez said, noting how the attacks prey on the victim’s sense of urgency to pull off the operation.
Cofense, in a report published this week, said the hospitality sector has been at the receiving end of a “well-crafted and innovative social engineering attack” that’s designed to deliver stealer malware such as Lumma Stealer, RedLine Stealer, Stealc, Spidey Bot, and Vidar.
“At the moment, the campaign only targets the hospitality sector, primarily luxury hotel chains and resorts, and uses inducements related to that sector such as booking requests, reservation changes and special requests,” Cofense said.
“The matching of lures for both reconnaissance and phishing emails is tailored accordingly and well thought out.”
The enterprise phishing threat management firm said it has also spotted malicious HTML attachments that are intended to carry out browser-within-the-browser (BitB) attacks by serving up innocuous pop-up windows that alert email recipients. They were tempted to provide their Microsoft credentials.
These findings indicate that threat actors are constantly finding new ways to infiltrate unsuspecting targets. Users should avoid clicking on unwanted links even if they appear legitimate, be suspicious of urgent or threatening messages demanding immediate action, and check URLs for indicators of deception.
