A new ongoing campaign called EleKtra-Leak has turned its focus to Amazon Web Services (AWS) identity and access management (IAM) credentials exposed within public GitHub repositories to facilitate cryptojacking activities.
“As a result of this, the threat actor associated with the campaign was able to create multiple AWS Elastic Compute (EC2) instances that they used for wide-ranging and long-lasting cryptojacking operations,” Palo Alto Networks Unit 42 researchers William Gamazo and Nathaniel Quist said in a technical report.
The operation, which has been active since at least December 2020, is designed to mine Monero from 474 unique Amazon EC2 instances between August 30 and October 6, 2023.
A standout aspect of the attacks is the automated targeting of AWS IAM credentials within four minutes of their initial exposure on GitHub, indicating that threat actors are programmatically cloning and scanning the repository to capture exposed keys.
Adversaries have also been observed blocking AWS accounts that propagate IAM credentials, possibly in an effort to prevent further analysis.
There is evidence to suggest that the attacker may also be linked to another cryptojacking campaign disclosed by Intezer in January 2021, which was aimed at targeting poorly secured Docker services using similar bespoke mining software.
Part of the success of the campaign lies in the exploitation of blindspots in GitHub’s latent scanning feature and AWS’s AWSCompromisedKeyQuarantine policy, to flag and prevent misuse of compromised or exposed IAM credentials to run or start EC2 instances.
While the quarantine policy is enforced within two minutes of AWS credentials becoming publicly available on GitHub, it is suspected that the keys are being exposed through an as-yet undetermined method.
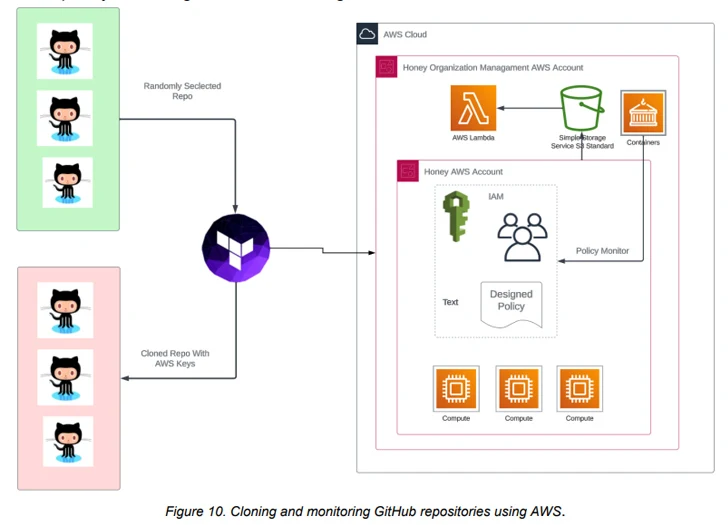
Unit 42 states that “A threat actor may be able to find exposed AWS keys that are not automatically detected by AWS and subsequently take control of these keys outside of the AWSCompromisedKeyQuarantine policy.”
In the attack chains discovered by the cybersecurity company, the stolen AWS credentials are used to perform an account reconnaissance operation, followed by creating AWS security groups and launching multiple EC2 instances across various regions from behind a virtual private network (VPN).
Cryptomining operations are conducted on c5a.24xlarge AWS instances due to their higher processing power, allowing its operators to mine more cryptocurrencies in less time.
The mining software used to carry out cryptojacking is fetched from a Google Drive URL, highlighting a pattern of malicious actors leveraging the trust associated with widely used applications to fly under the radar.
“The type of Amazon Machine Images (AMI) that the threat actor used was also specific,” the researchers said. “The images identified were private and not listed in the AWS Marketplace.”
To mitigate such attacks, organizations that accidentally expose AWS IAM credentials are recommended to immediately revoke any API connections using the keys, remove them from the GitHub repository, and audit GitHub repository cloning events for any suspicious operations.
“A threat actor could detect and launch a full-scale mining campaign within five minutes of having AWS IAM credentials exposed in a public GitHub repository,” the researchers said. “Despite successful AWS quarantine policies, the number and frequency of compromised victim accounts in the campaign continues to fluctuate.”
